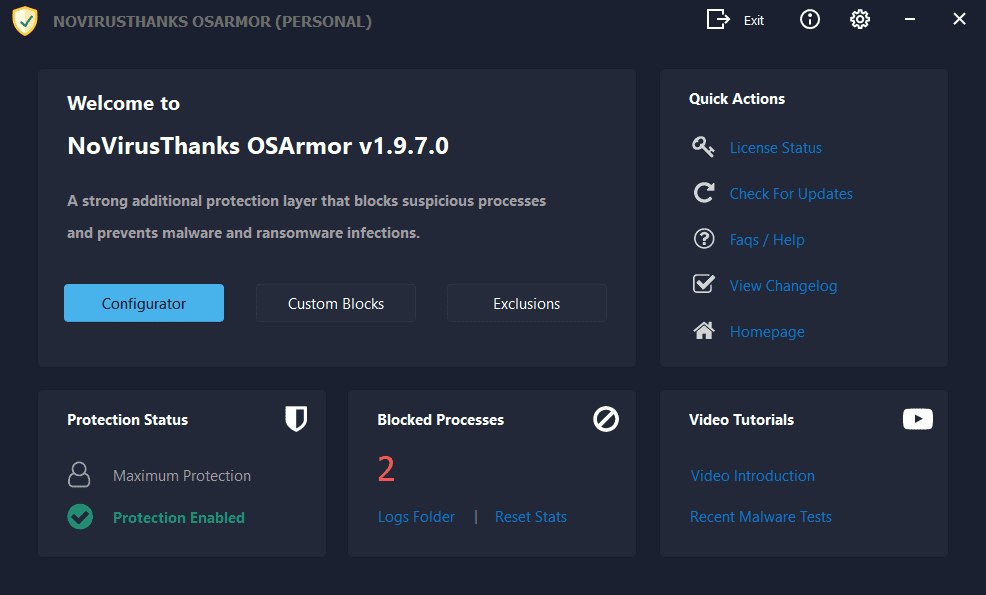
Prevent Malware & Ransomware
OSArmor is a Windows OS application that monitors and blocks suspicious processes behaviors
to prevent infections by malware, ransomware, and other threats.
This tool analyzes parent processes and prevents, for example, MS Word from running cmd.exe or powershell.exe. It
prevents ransomware from deleting shadow copies of files via vssadmin.exe, blocks processes with double file
extensions (i.e invoice.pdf.exe), blocks USB-spreading malware, and much more. It is lightweight,
requires zero user input and
protects your system while running in the background.
In combination with OSArmor you can
also use SysHardener to harden even more Windows OS settings.
For Windows 7 SP1, 8, 10, 11 (32 & 64-bit)