Why OSArmor? Read Here
OSArmor plays an important role in improving the security of your computer.
It adds a powerful layer of defense to prevent known and unknown threats by accurately
analyzing processes behaviors. Here are some of its key features:
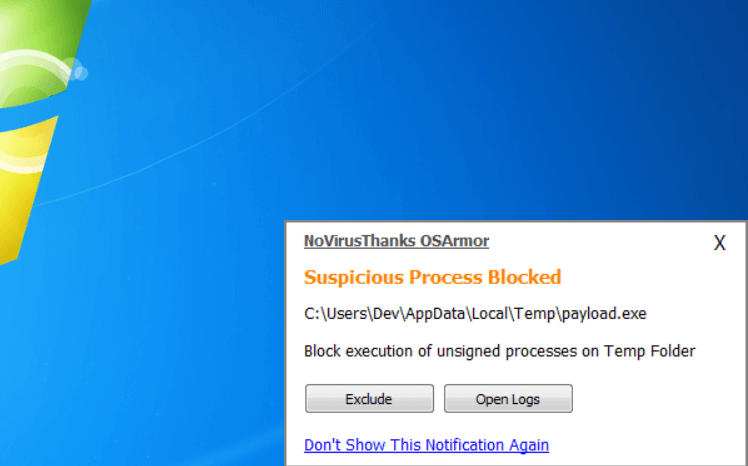
Block Suspicious Processes
OSArmor monitors and block suspicious processes activities to prevent a possible malware infection. It uses very complex rules to decide what process behavior is considered suspicious or known malicious. If a process does something suspicious or triggers OSArmor rules, it will be automatically blocked.

Prevent Ransomware
Ransomware, malware and other pests are commonly delivered on the victim's computer via "third-party" methods, such as via emails, maldocs, scripts, emotet, and so on. OSArmor can prevent a ransowmare or malware infection by blocking the delivery method used to execute and install the malware in the system.
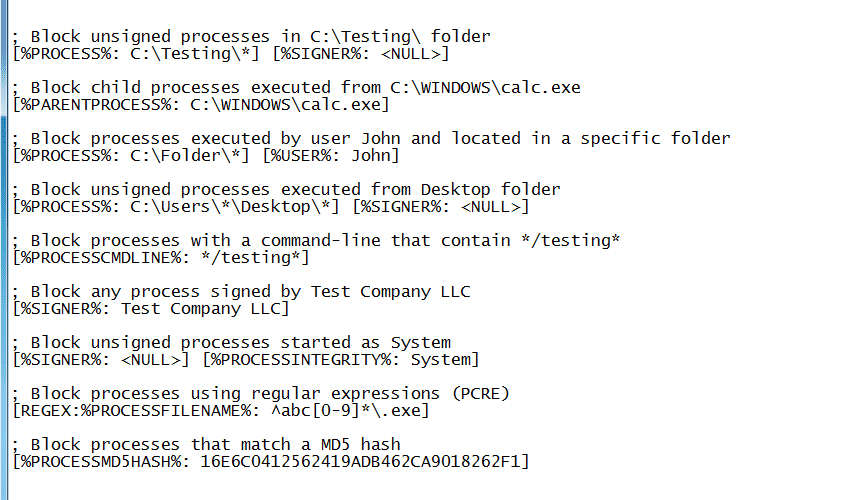
Write Custom Block Rules
With OSArmor you can write your own rules to block specific process behaviors. For example, you can block unsigned processes in specific folders, you can block new LOLBins behaviors, you can block processes with a specific file name or executed by a particular parent process, possibilities are mostly "infinite".
More Information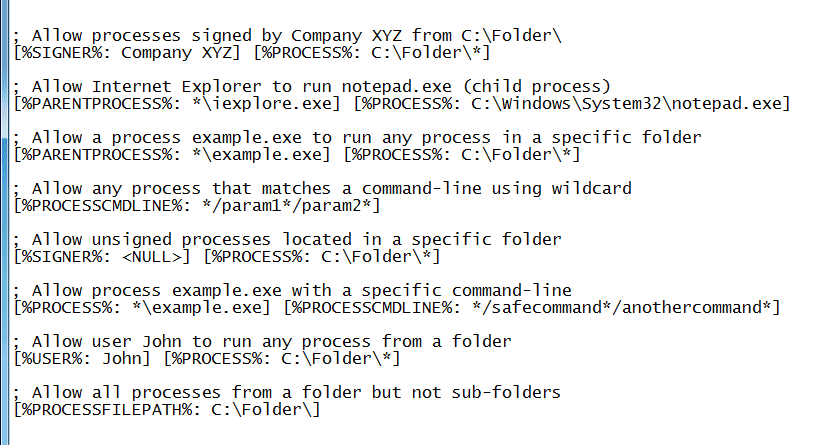
Write Exclusion Rules
The same way as you can write custom block rules, you can also write exclusion rules to allow specific process behaviors. This is useful to allow safe process behaviors or exclude a process behavior that triggers a block rule. For example, you can allow processes signed by Company XYZ, or processes with a particular command-line.
More Information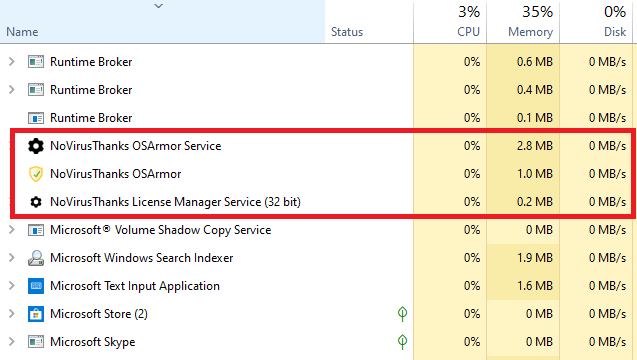
Low on System Resources
The program should not use more than 50 MB of memory and CPU usage is very low even if you run many applications at the same time or "heavy" applications. You will not even notice that OSArmor is running in your system and is keeping it safe with its complex process behavioral analysis engine.
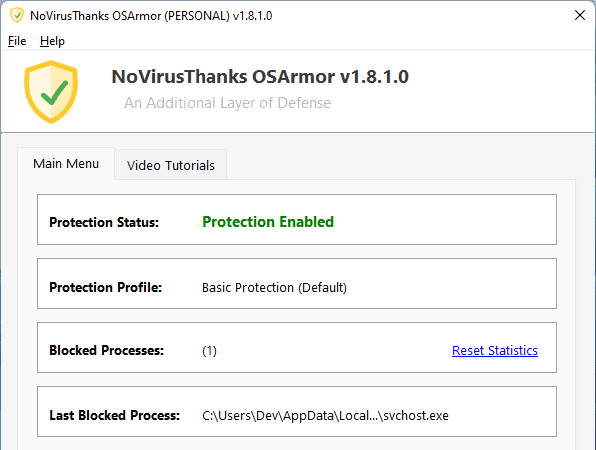
Another Layer of Defense
OSArmor is a great ally to fight malware and can catch what others didn't. If something gets past your antivirus software then there is OSArmor that adds an additional layer of defense by blocking suspicious process behavior. Having different layers of protection will definitely increase the security level of your system.
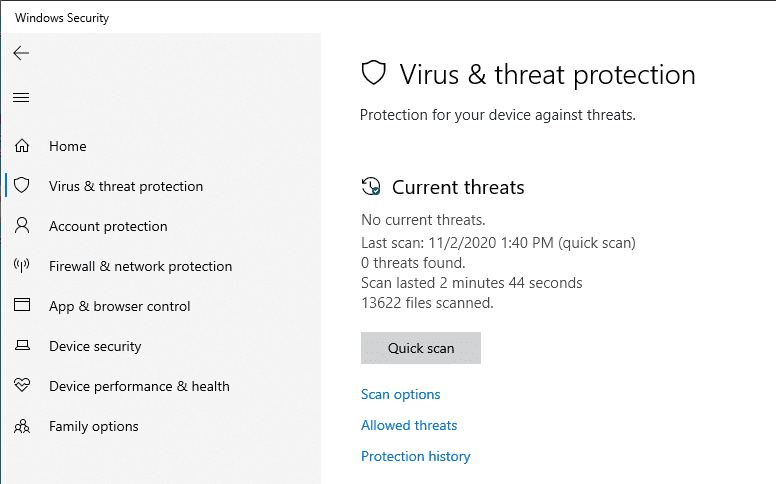
Windows Defender-Friendly
Many Windows 10 users are using OSArmor alongside with the pre-installed Windows Defender antivirus. They can work together without problems and are a good "combo" to improve the protection from ransomware, malware and other online threats. OSArmor works fine also with mostly any other security software.
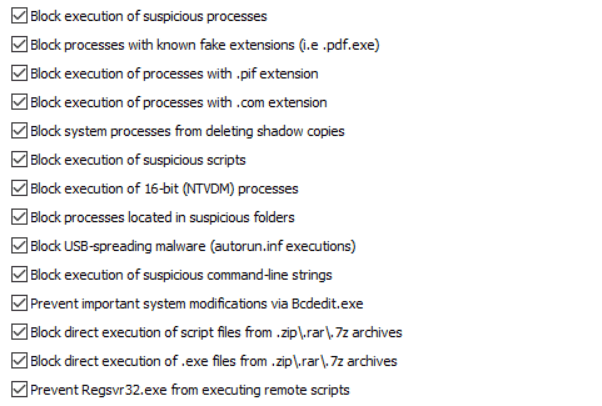
User-Selectable Rules
We added more than 100+ pre-configured rules in Configurator GUI that can be easily enabled/disabled with a mouse click. These rules include protection for Microsoft Office apps, block of JS/VBS/VBE/WSF scripts, bock of suspicious command-lines, block of processes in suspicious locations, and much more.

1000+ Smart Internal Rules
Along with the pre-configured and selectable rules, OSArmor uses thousands of internal rules to detect known and not-yet-known suspicious process activities. These complex and smart internal rules are very effective in blocking current (and future) malicious process behavior by using predictive analysis.
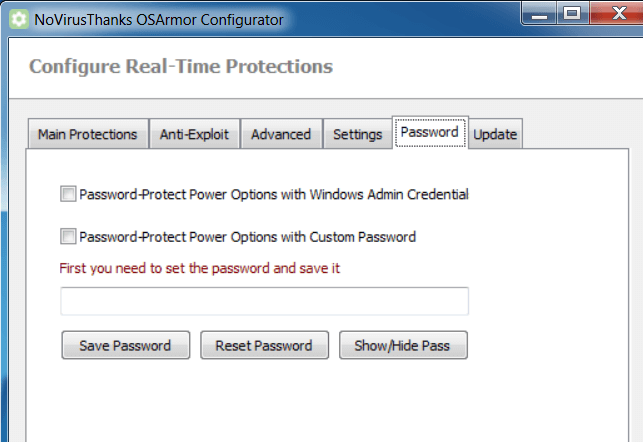
Password-Protect Options
As requested by system administrators, we added options to password-protect power options with Windows Admin credentials or with a custom password of your choice. This is useful if you don't want other users to be able to disable OSArmor protection, or edit OSArmor settings, or exclude/allow a blocked event.
Auto-Update Option
From version 1.5 we introduced an option to enable automatic updating of the product. This is useful for users that want to make sure they are always using the latest version of the product without the need to manually download and install the new version.
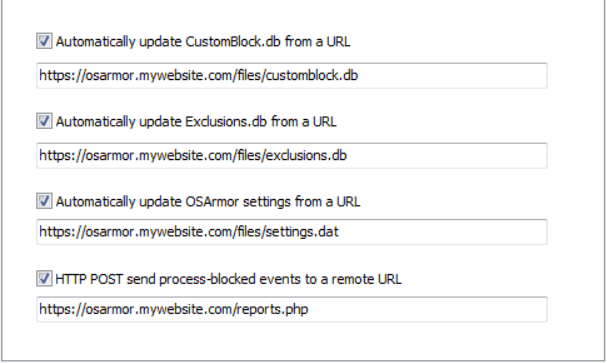
Remote Management
The Enterprise version includes features to simplify the management of OSArmor from a single location: you can auto-update CustomBlock.db (your custom block rules) and Exclusions.db files from a URL, auto-update of OSArmor settings from a URL, and even HTTP POST process-blocked events to a remote URL.